Head Office: 24B Amodu Tijani Close Victoria Island Lagos, Nigeria.
- Tigerlogic Africa
- Accelerate and Protect Networks
Accelerate and Protect Networks
Securing Your Network Infrastructure with Advanced Threat Protection
As cyber threats become more sophisticated, organizations must deploy robust network security and access control measures to safeguard their IT environments. TigerLogic Africa’s Network Security & Access Control solutions provide end-to-end protection, ensuring your business remains resilient against attacks while enabling seamless, secure access.
Common Challenges We Solve
- Ransomware and Advanced Persistent Threats (APTs) continue to evolve, bypassing traditional security measures.
- Organizations struggle with securing remote access and implementing Zero Trust policies.
- Email phishing attacks and malware-based threats exploit vulnerabilities in enterprise networks.
TigerLogic Africa’s security solutions mitigate these risks with AI-driven analytics, next-generation firewalls, and real-time threat detection.
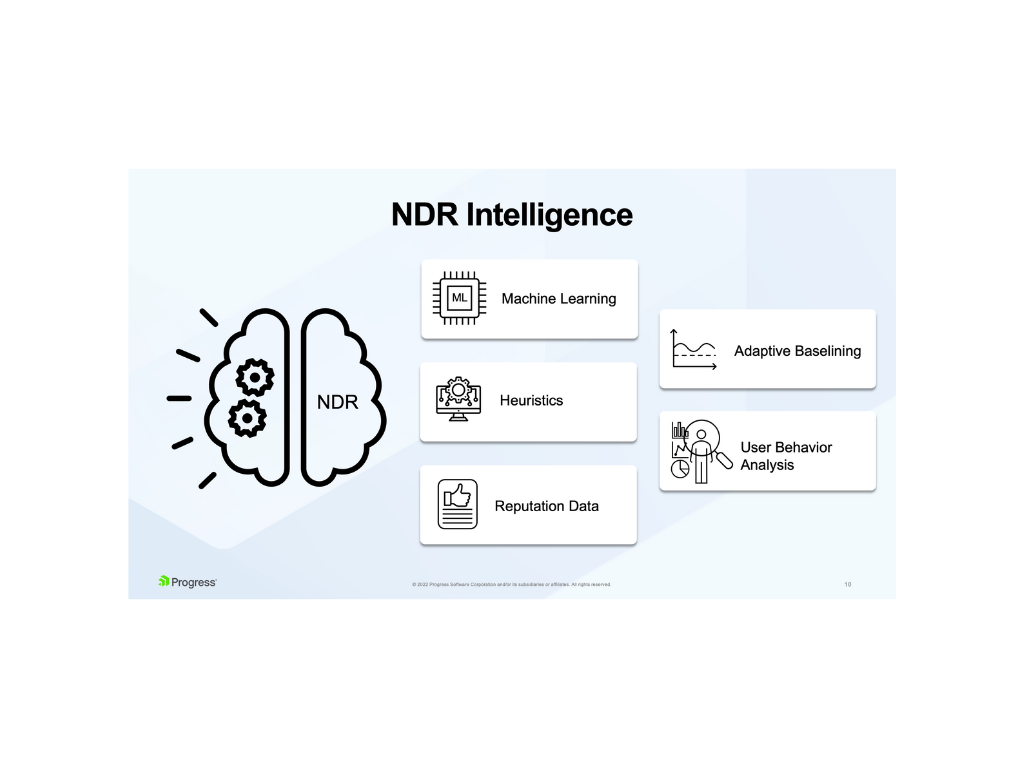
Network Detection & Response (NDR)
- AI-Powered Threat Detection: Identify anomalies and advanced threats in real time.
- Automated Incident Response: Rapid containment of malicious activities before they spread.
- Deep Network Visibility: Continuous monitoring and analysis of traffic patterns.
Next-Generation Firewall (NGFW) & IDS/IPS
- Intrusion Prevention Systems (IPS): Proactively block known and emerging threats.
- Application-Aware Firewalling: Granular control over applications and user activities.
- Zero Trust Network Enforcement: Adaptive security policies based on user identity and behavior.

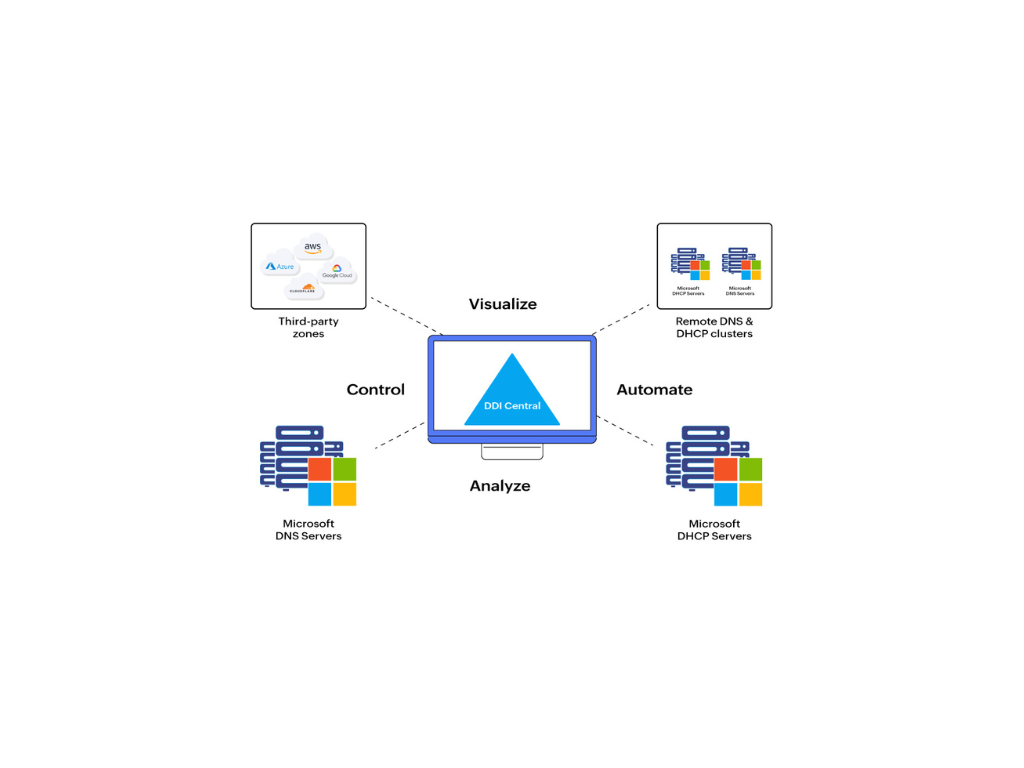
Secure DNS, DHCP, and IPAM (DDI)
- DNS Security & Threat Intelligence: Prevent domain-based cyberattacks and DNS tunneling.
- Automated IP Address Management: Improve visibility and control over IP infrastructure.
- Dynamic Host Configuration Protocol (DHCP) Security: Reduce vulnerabilities in IP allocation.
Email Security Gateway
- Advanced Phishing Protection: Block email threats such as BEC, malware, and spoofing.
- Email Encryption & Data Loss Prevention (DLP): Safeguard sensitive communications.
- AI-Powered Spam Filtering: Prevent unwanted and malicious emails from reaching inboxes.

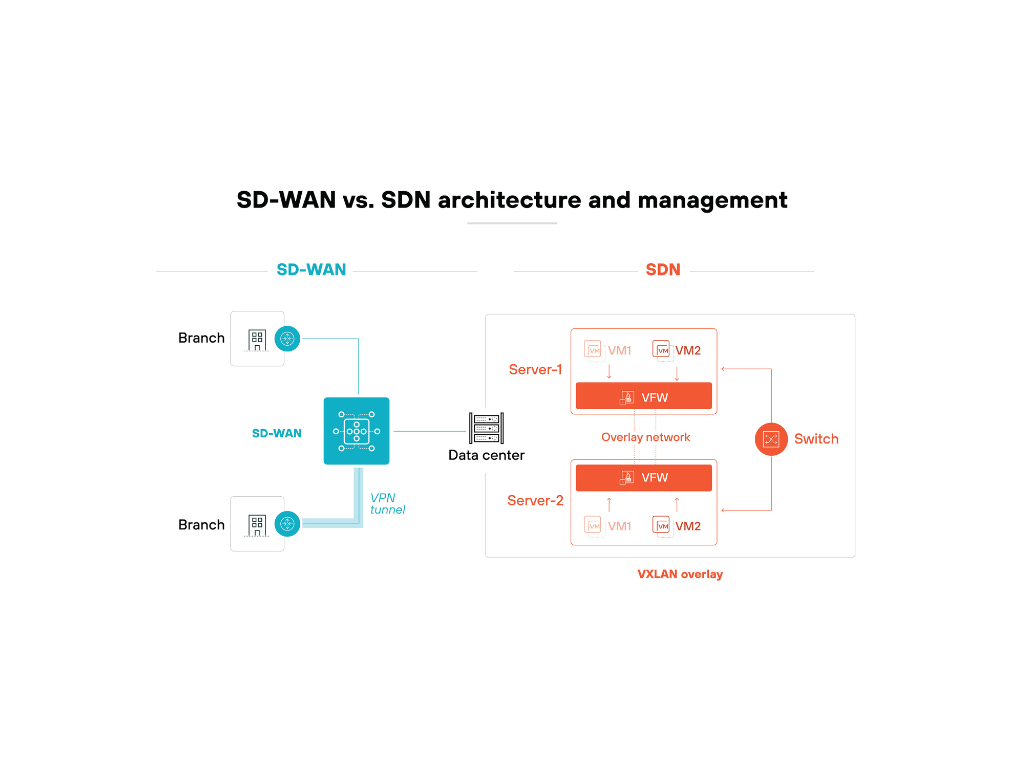
Software-Defined Networking (SD-WAN)
- Secure Cloud Connectivity: Optimize and secure WAN traffic across hybrid cloud environments.
- Application-Aware Routing: Ensure high-performance connectivity for business-critical applications.
- Zero-Touch Provisioning: Simplified deployment and centralized network management.
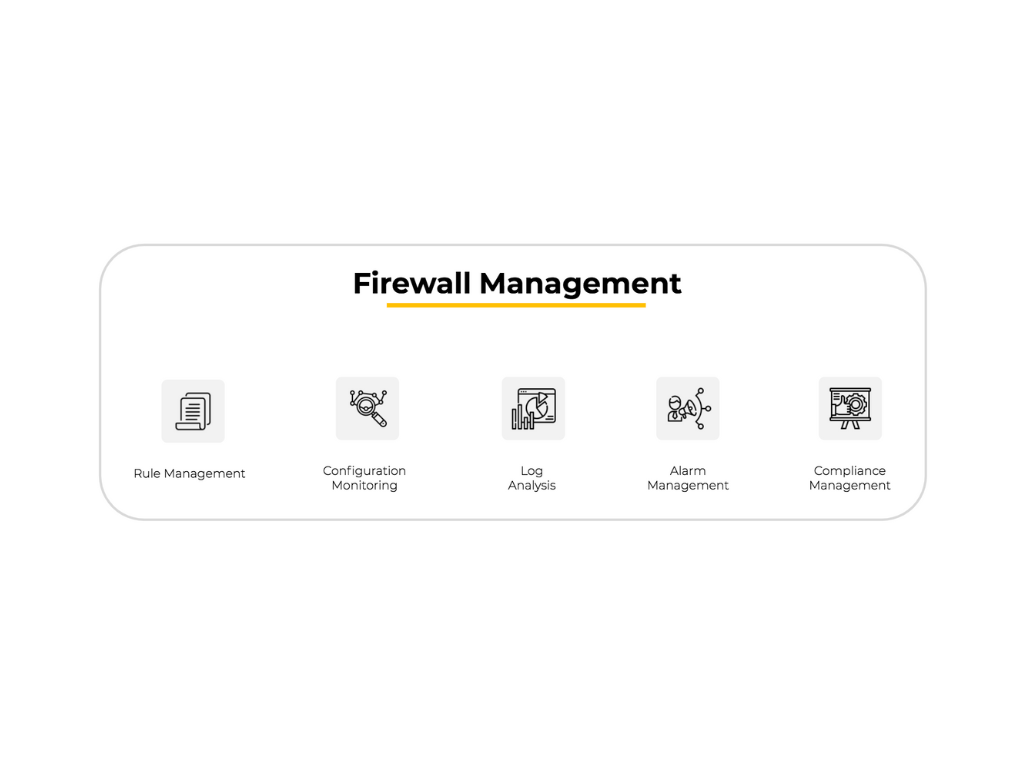
Firewall Management Solutions
- Policy Optimization & Compliance: Ensure firewall rules align with security best practices.
- Automated Rule Analysis & Change Management: Reduce misconfigurations and security gaps.
- Centralized Firewall Monitoring: Gain real-time insights into firewall health and performance.
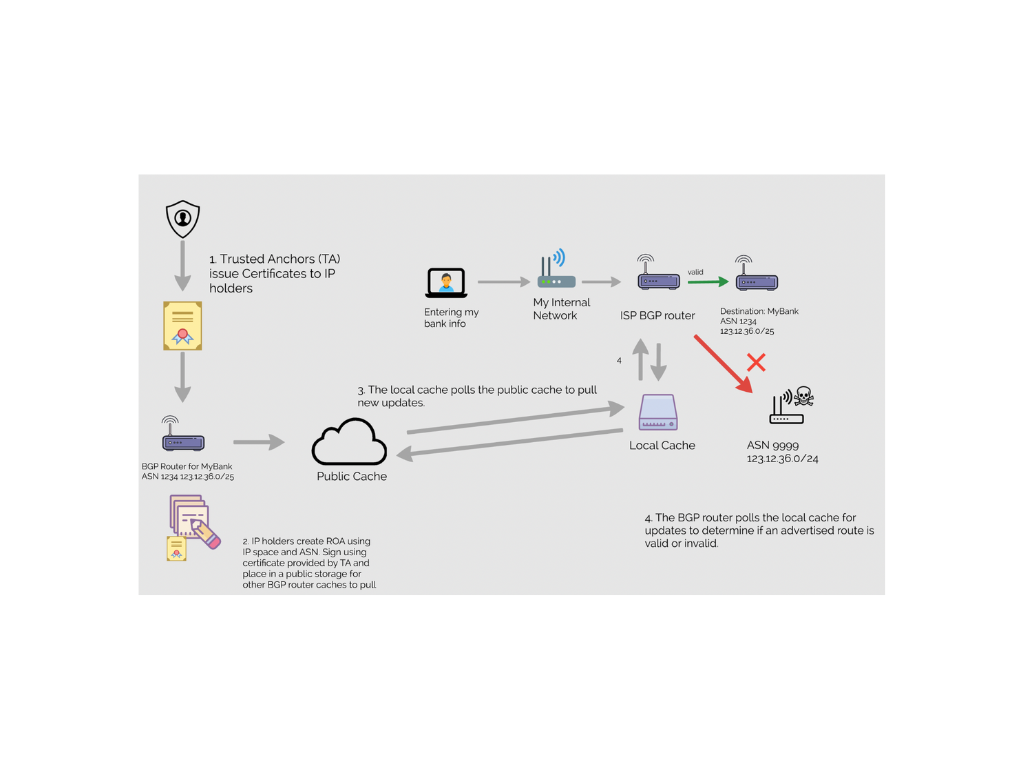
IP Integrity Solutions
- Spoofing & Hijacking Protection: Prevent unauthorized manipulation of network identities.
- Secure Border Gateway Protocol (BGP) Implementations: Protect against route hijacking.
- Real-Time Traffic Validation: Ensure legitimate communication across IP networks.
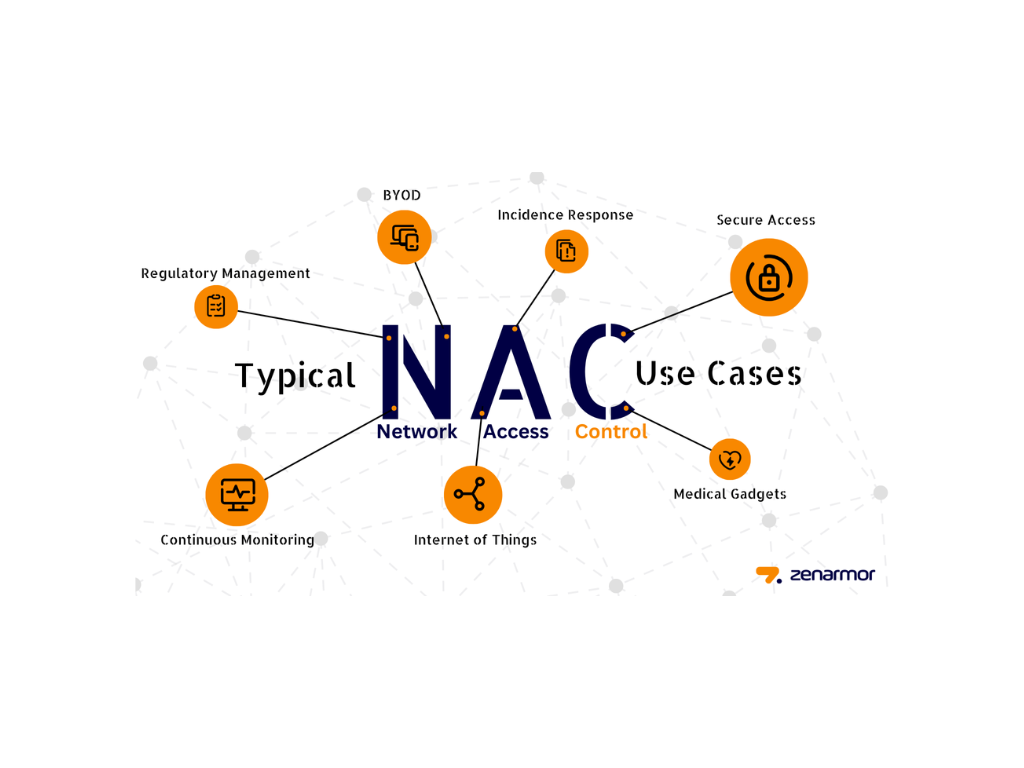
Network Access Control (NAC)
- Device Authentication & Compliance Enforcement: Verify device security posture before granting access.
- User-Based Access Policies: Control access based on identity and role-based permissions.
- Automated Quarantine & Remediation: Detect and isolate non-compliant or compromised devices.
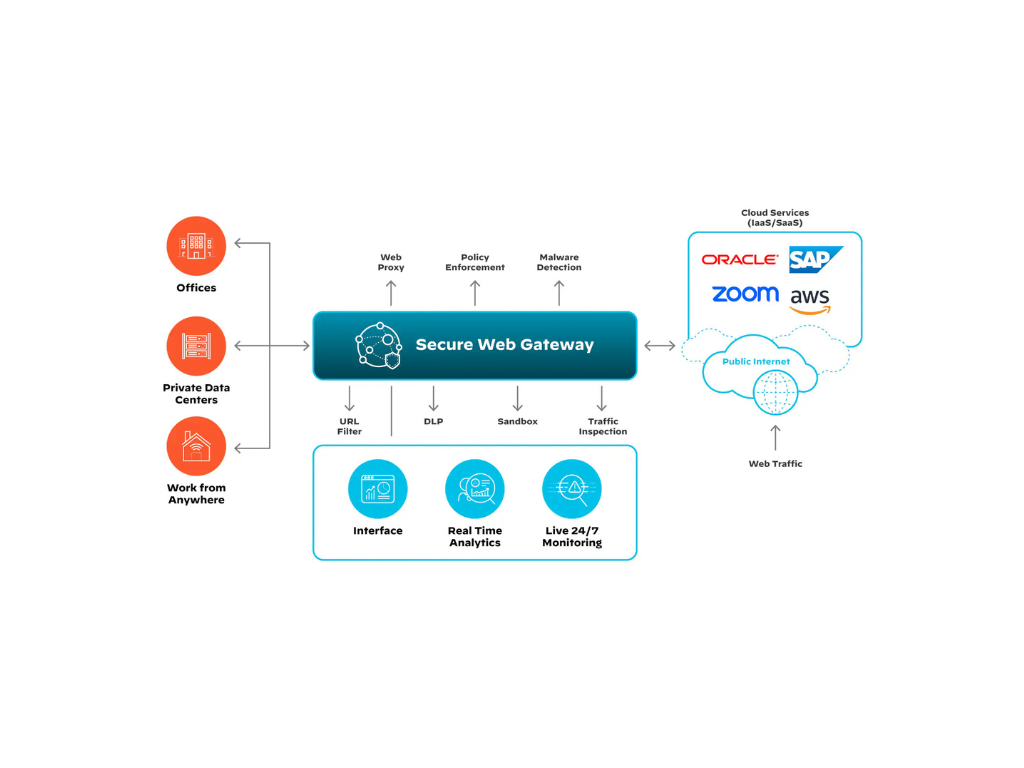
Secure Web Gateway (SWG)
- Web Content Filtering & Malware Prevention: Block malicious websites and harmful downloads.
- Cloud-Based & On-Premises Deployment: Flexible protection for users across any environment.
- Threat Intelligence Integration: Leverage real-time global threat insights for enhanced security.
Secure Your Business Today
Protect your network from evolving cyber threats.
Contact TigerLogic Africa to discuss a customized network security strategy.
Head Office
-
-
24B Amodu Tijani Close, Victoria Island Lagos, Nigeria
Ghana
-
-
9th Floor Emporium Building Movenpick Ambassador Hotel Independence Avenue Accra, Ghana
Kenya
-
-
PentOffice, The Mirage Tower 2, Westlands Waiyaki Way Nairobi, Kenya
