Head Office: 24B Amodu Tijani Close Victoria Island Lagos, Nigeria.
- Tigerlogic Africa
- Information Systems Protection
Information Systems Protection
Protecting Critical Business Data and Endpoints Against Evolving Threats
With cyber threats targeting cloud environments, business data, and endpoints at an alarming rate, organizations must strengthen their security posture. TigerLogic Africa’s Data & Endpoint Security solutions ensure robust protection against data breaches, ransomware, and identity theft.
Common Challenges We Solve
- Increasing data breaches and ransomware attacks threaten sensitive business information.
- Businesses struggle to enforce endpoint security policies across remote and hybrid work environments.
- Cloud environments are exposed to misconfigurations and unauthorized access risks.
TigerLogic Africa’s security solutions mitigate these risks with AI-driven analytics, identity-based controls, and real-time threat detection.
Data Security
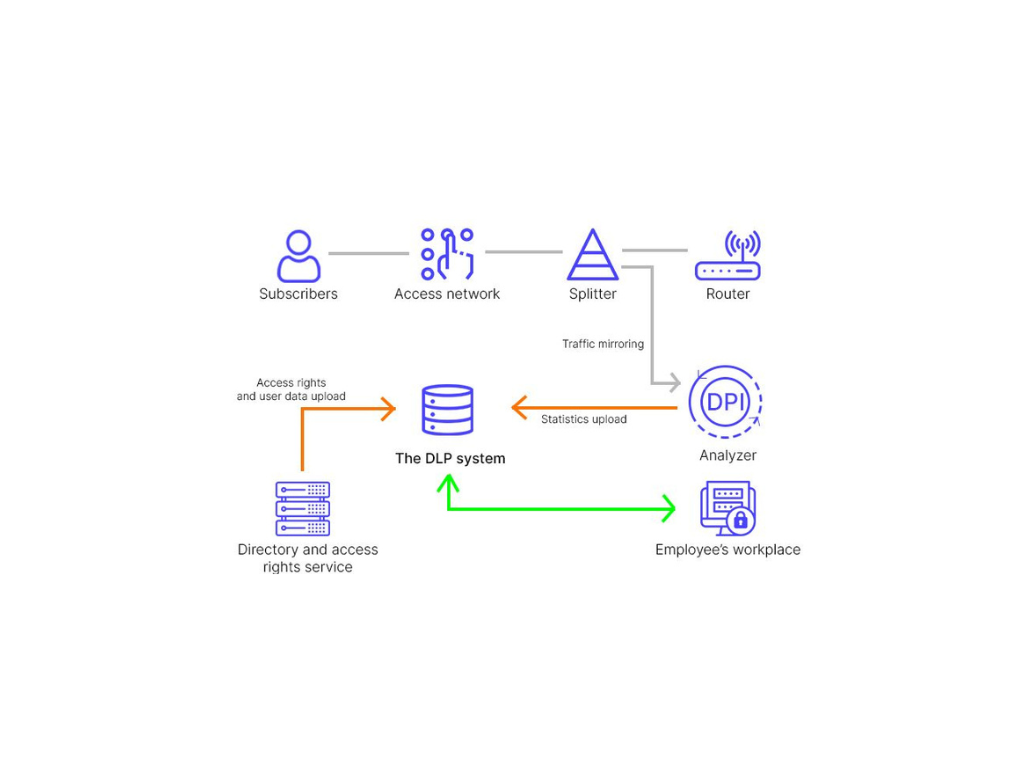
- Encryption & Data Loss Prevention (DLP): Secure sensitive business data against unauthorized access and data exfiltration.
- Data Classification & Governance: Implement policies for data integrity, compliance, and structured management.
- Secure Data Storage & Backup: Protect business-critical data with automated backup and recovery solutions.
Cloud Security
- Cloud Access Security Broker (CASB): Enforce security policies and protect cloud applications from unauthorized access.
- Secure Cloud Workloads: Monitor and defend cloud environments against cyber threats and misconfigurations.
- Identity & Compliance Controls: Ensure cloud security with policy-based access controls and regulatory compliance frameworks.

Endpoint Security & Security Operations
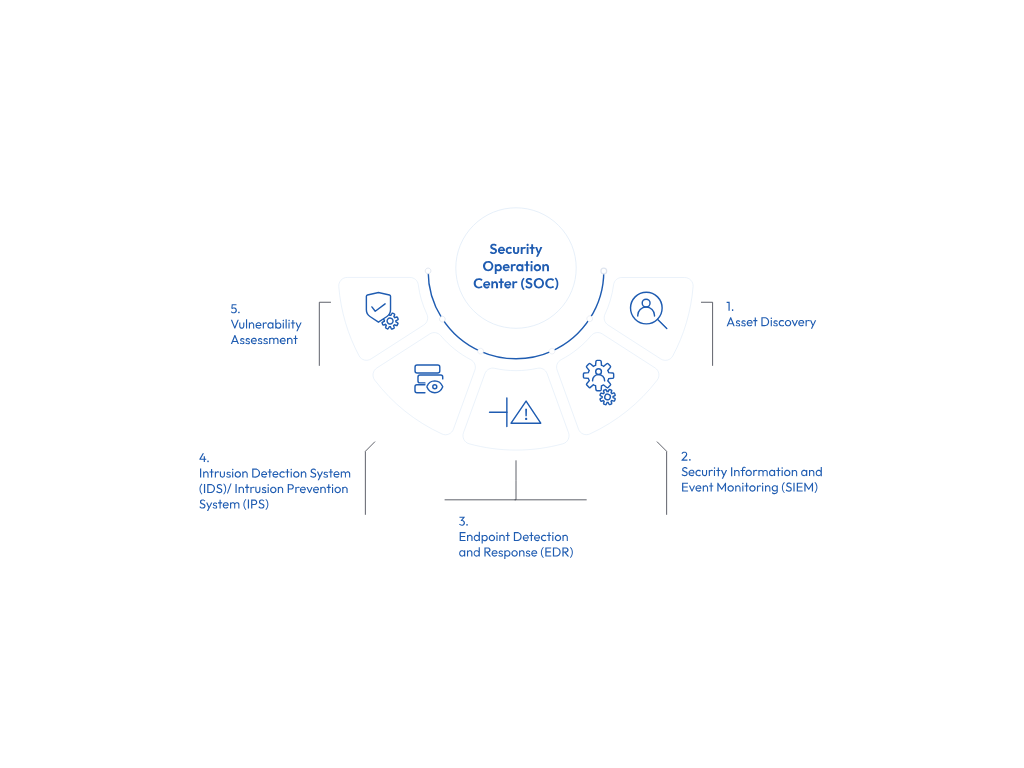
- Endpoint Detection & Response (EDR/XDR): Detect, investigate, and remediate endpoint threats in real-time.
- Next-Generation Antivirus (NGAV): Defend endpoints with AI-driven malware detection and prevention.
- Security Operations Center (SOC) Integration: Centralized threat monitoring and incident response for endpoints.
Identity Security
- Identity & Access Management (IAM): Ensure secure user authentication with multi-factor authentication (MFA) and role-based access control.
- Privileged Access Management (PAM): Prevent unauthorized access by managing and monitoring privileged accounts.
- Zero Trust Security Framework: Enforce least privilege access and continuous identity verification.

Secure Your Business Today
Ensure the security of your data and endpoints.
Contact TigerLogic Africa to discuss a tailored protection strategy for your organization.
Head Office
-
-
24B Amodu Tijani Close, Victoria Island Lagos, Nigeria
Ghana
-
-
9th Floor Emporium Building Movenpick Ambassador Hotel Independence Avenue Accra, Ghana
Kenya
-
-
PentOffice, The Mirage Tower 2, Westlands Waiyaki Way Nairobi, Kenya
