Head Office: 24B Amodu Tijani Close Victoria Island Lagos, Nigeria.
- Tigerlogic Africa
- Accelerate and Protect Applications
Accelerate and Protect Applications
Securing Applications and APIs Against Emerging Cyber Threats
Modern businesses rely on applications and APIs for seamless operations, but these assets are prime targets for cyber threats. TigerLogic Africa’s Application & API Security solutions protect your digital environment from advanced attacks, ensuring secure and high-performance application delivery.
Common Challenges We Solve
- API vulnerabilities and misconfigurations lead to data breaches and unauthorized access.
- Automated bot attacks exploit security gaps in applications, leading to fraud and data scraping.
- DDoS and web-based attacks threaten application availability and performance.
TigerLogic Africa’s security solutions mitigate these risks with AI-powered analytics, real-time monitoring, and proactive threat mitigation.
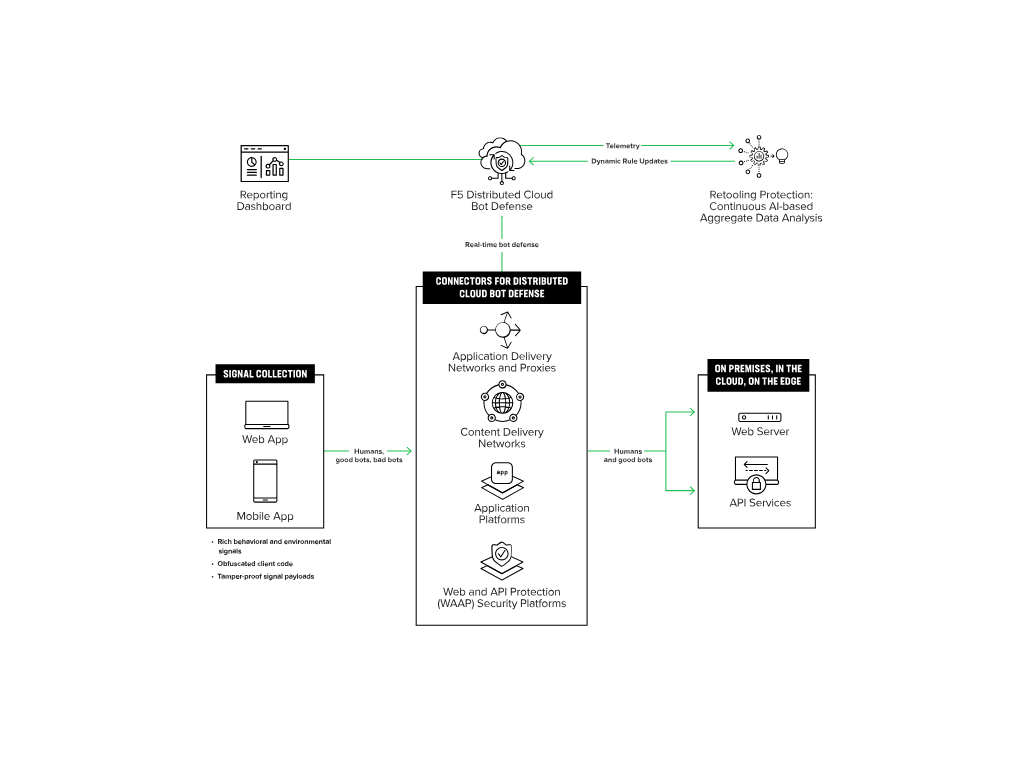
Bot Defense
- Automated Threat Protection: Identify and block bot-driven attacks such as credential stuffing and web scraping.
- Behavioral Analytics: Use AI-driven analysis to distinguish between legitimate users and malicious bots.
- Real-Time Response: Automatically mitigate bot threats without disrupting legitimate traffic.
Web Application Firewall (WAF)
- Threat Prevention: Protect applications from OWASP Top 10 vulnerabilities, including SQL injection and XSS attacks.
- Custom Security Rules: Fine-tune security policies to meet your application’s specific requirements.
- Cloud & On-Premises Deployment: Flexible WAF solutions for hybrid IT environments.

API Security & Management
- API Gateway Protection: Secure API endpoints with authentication, rate limiting, and encryption.
- Runtime Threat Detection: Monitor API traffic for anomalies and potential attacks.
- Access Control & Governance: Implement zero-trust policies for API interactions.
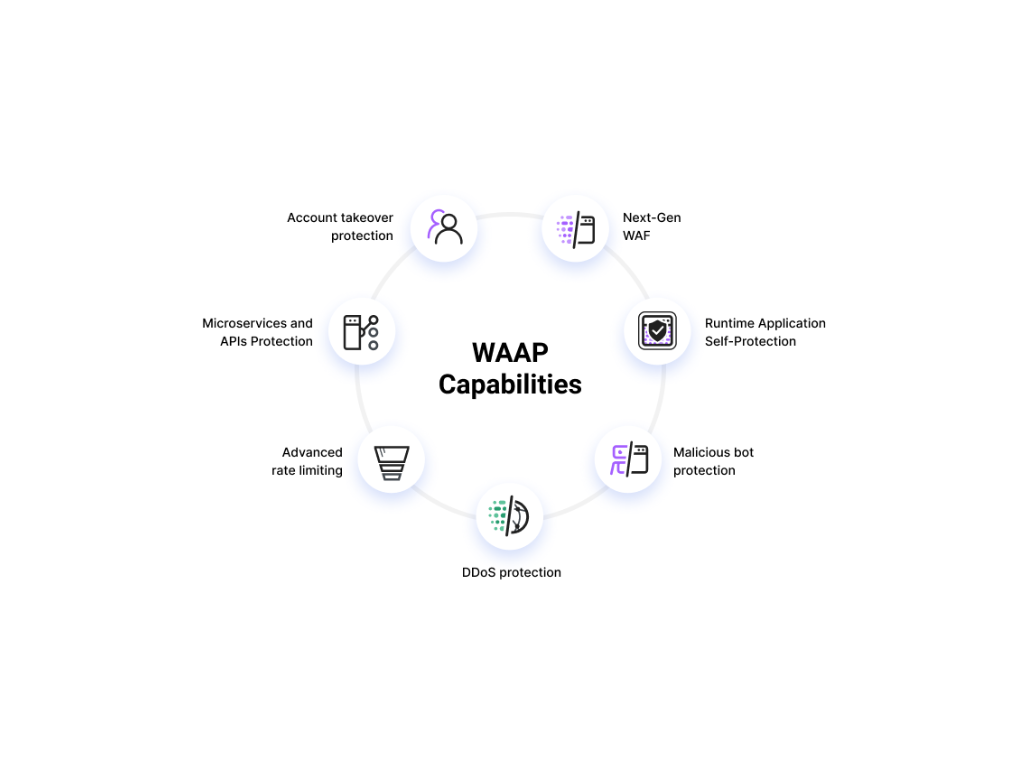
Cloud Web Application & API Protection
- Integrated Security for Web & APIs: Holistic protection against DDoS, bot attacks, and API abuse.
- Threat Intelligence & Automated Mitigation: Leverage AI-driven threat detection to prevent breaches.
- Scalable Security Architecture: Adapt protection measures based on traffic demand.

Access Management Solutions
- Single Sign-On (SSO) & Multi-Factor Authentication (MFA): Strengthen user authentication.
- Adaptive Authentication: Implement risk-based access control based on user behavior.
- Privileged Access Management (PAM): Prevent unauthorized access to critical applications.
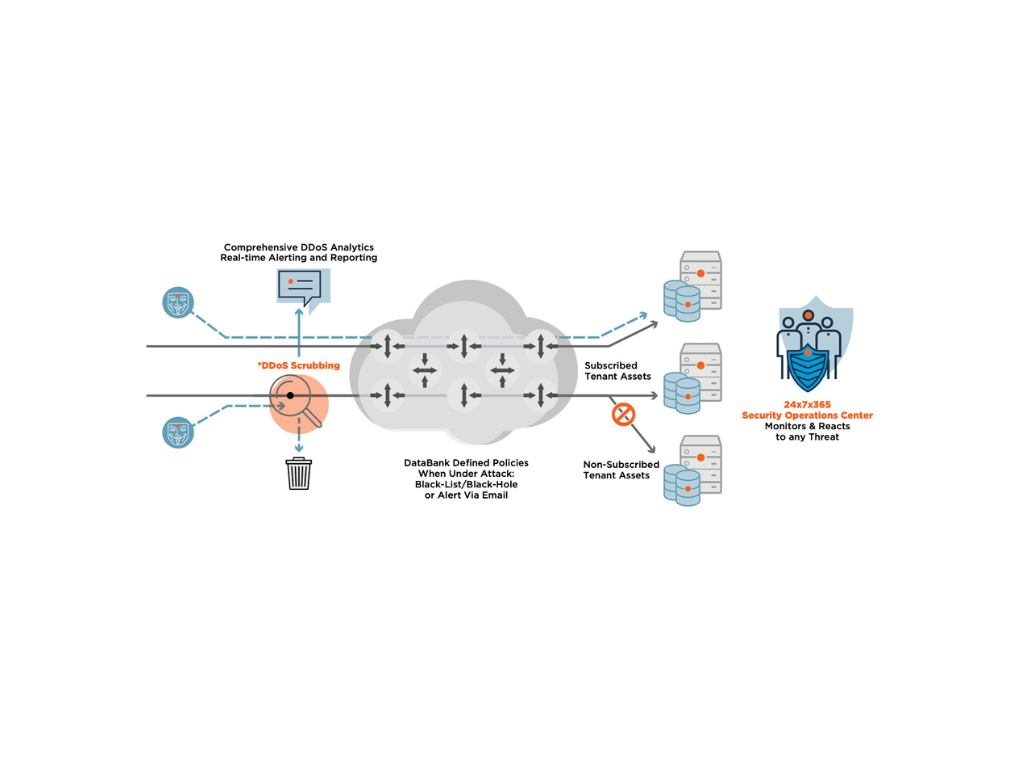
DDoS Mitigation Solutions (Anti-DDoS)
- Real-Time Attack Detection: Identify and mitigate large-scale distributed denial-of-service (DDoS) threats.
- Scalable Defense Mechanisms: Handle high-volume attacks without impacting performance.
- Global Traffic Scrubbing: Redirect malicious traffic before it reaches your network.
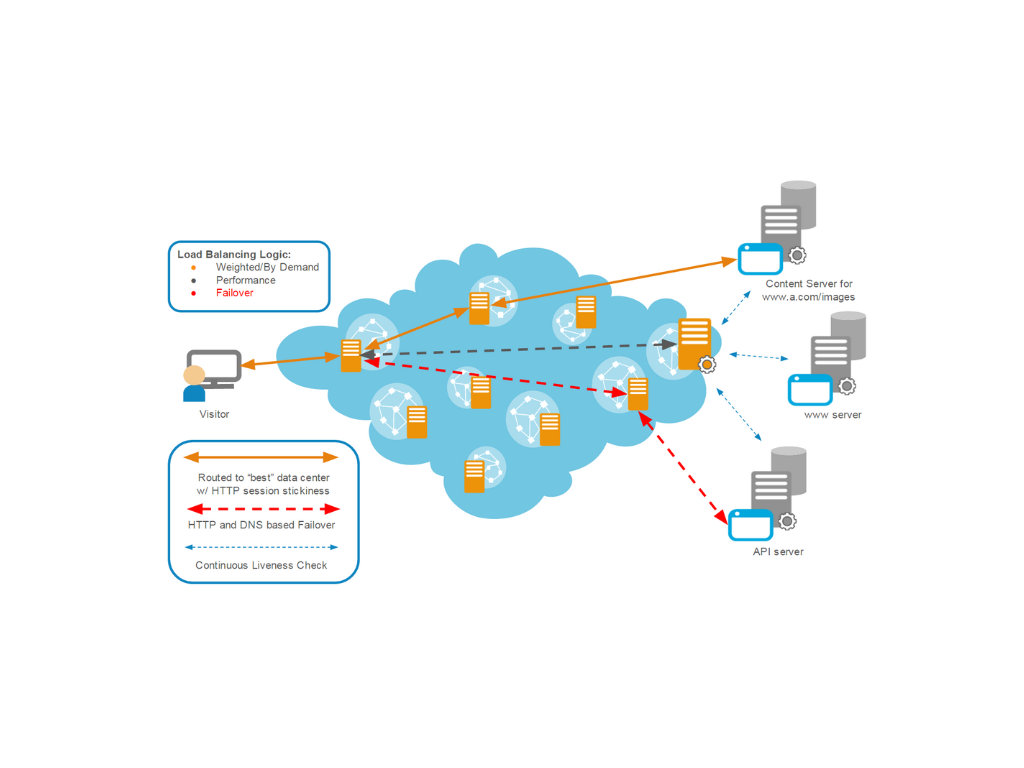
Application Delivery Controllers (ADC)
- Load Balancing & Performance Optimization: Ensure reliable application performance under heavy traffic.
- End-to-End Encryption & Security Policies: Secure data transmission across applications.
- Traffic Management & Fault Tolerance: Improve application availability and reduce downtime.
Secure Your Business Today
Protect your applications and APIs from evolving cyber threats
Contact TigerLogic Africa to discuss a customized application security strategy.
Head Office
-
-
24B Amodu Tijani Close, Victoria Island Lagos, Nigeria
Ghana
-
-
9th Floor Emporium Building Movenpick Ambassador Hotel Independence Avenue Accra, Ghana
Kenya
-
-
PentOffice, The Mirage Tower 2, Westlands Waiyaki Way Nairobi, Kenya
